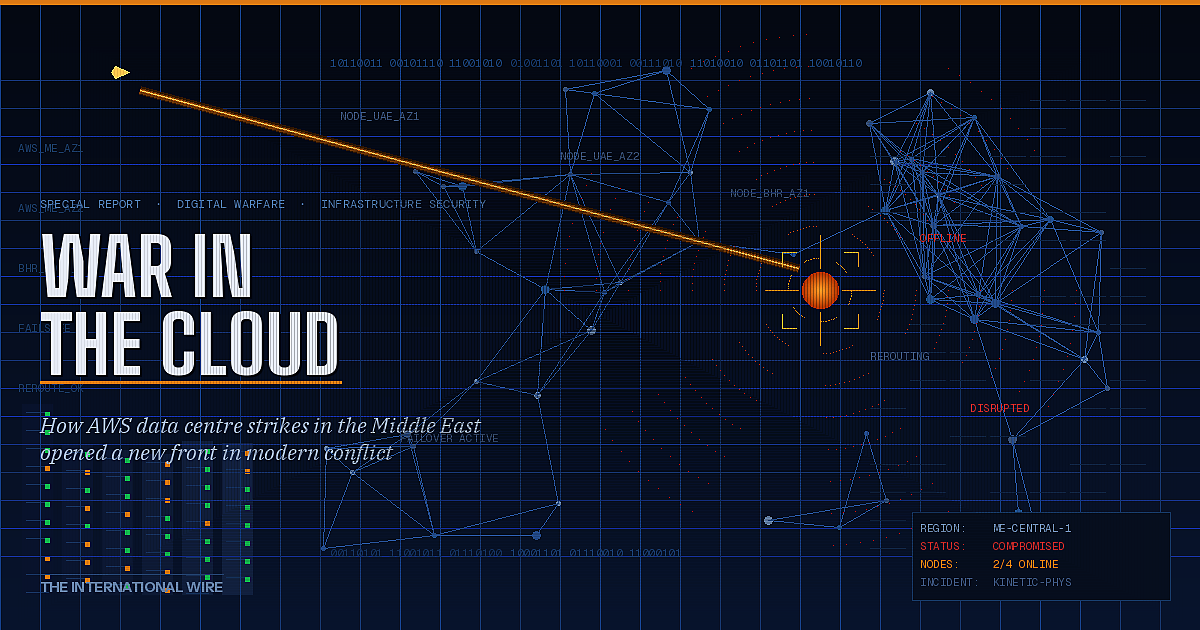
How the AWS Data Centre Strikes in the Middle East Opened a New Front in Modern Conflict
The drone strikes that hit Amazon Web Services data centres in the United Arab Emirates, and damaged a third facility in Bahrain, will be studied by military strategists, technology executives, and policymakers for years to come. Not because of the immediate disruption they caused — the cloud outages, while significant, were resolved within hours — but because of what they represent: the first confirmed physical targeting of hyperscale commercial cloud infrastructure during a major geopolitical conflict.
In a single operation, the long-standing assumption that the cloud exists somewhere above and beyond the friction of geopolitical conflict was shattered. The servers went dark. The buildings burned. And the global technology industry was forced to confront a reality it had long preferred to defer: the cloud is, in the end, a collection of buildings — and buildings can be bombed.
For the first time in a major conflict, the physical foundations of the global digital economy became a military target. The cloud, it turns out, has an address.
The implications extend well beyond the Gulf. If the targeting of hyperscale data centres becomes a normalised element of modern warfare — alongside strikes on oil refineries, power grids, and telecommunications towers — then the architecture of the global internet, the strategies of the technology industry, and the security posture of every government that has migrated its critical systems to the cloud must be fundamentally reconsidered.
This report examines what happened, why it happened, and what it means for the future of conflict, infrastructure, and the digital economy.
What Was Struck — and What Was Lost
The AWS facilities targeted in the UAE sit within the company’s Middle East (UAE) cloud region — a cluster of data centres that collectively serve thousands of enterprise customers, government agencies, and technology platforms across the Gulf, South Asia, and East Africa.
These are not ordinary server rooms. Modern hyperscale data centres are among the most complex and capital-intensive structures ever built — vast warehouse-scale facilities housing hundreds of thousands of servers, sustained by dedicated power substations delivering tens of megawatts of electricity, cooled by industrial-scale chilled water systems, and connected to the global internet via multiple high-capacity fibre routes.
The strikes damaged power distribution infrastructure and cooling systems in two UAE facilities. A third facility in Bahrain — part of the AWS Middle East (Bahrain) region, one of the company’s most significant cloud hubs in the area — sustained damage from a strike on an adjacent site, causing partial service disruption.
The immediate impact included outages across compute, storage, and database services for customers in the affected availability zones. Organisations that had implemented multi-region redundancy were able to reroute workloads with minimal interruption. Those that had not — smaller businesses, government agencies, and startups that had concentrated their infrastructure in a single regional cluster — experienced more prolonged disruption.
AWS and the UAE government declined to confirm the full scope of the damage, and the precise operational timeline for restoration remained unclear. But the technical community’s assessment was unambiguous: the strikes had successfully degraded hyperscale cloud services in a way that no purely digital cyber attack had previously achieved.
No ransomware campaign, no DDoS attack, no state-sponsored hacking operation has ever taken a hyperscale cloud region offline. A drone did it in minutes.
Why Data Centres Were Targeted: The Strategic Logic
The targeting of digital infrastructure did not happen arbitrarily. Military and intelligence analysts identify a coherent three-part strategic logic behind the strikes — one that reflects a sophisticated understanding of how modern economies and military operations actually function.
The first motivation is economic warfare at scale. A single hyperscale data centre serves not one organisation but thousands simultaneously. When a facility goes offline, the disruption cascades across an entire ecosystem of businesses, government services, financial platforms, and logistics networks. The economic damage inflicted per strike is therefore disproportionate to the physical scale of the attack — a characteristic that makes data centres exceptionally high-value targets by any military calculus.
The second motivation is the disruption of military and intelligence operations. The boundary between commercial and military cloud infrastructure has blurred considerably over the past decade. Western military organisations — including the United States Department of Defense, which operates a multi-billion dollar cloud contract with commercial providers — rely on hyperscale platforms for intelligence analysis, logistics coordination, satellite image processing, and battlefield communications. Degrading the commercial cloud in a contested region therefore carries direct military consequences, not merely economic ones.
The third motivation is geopolitical signalling of a particularly pointed kind. AWS is an American company. Its data centres flying the flag of the world’s dominant technology power in the heart of the Gulf. Striking those facilities sends a message that transcends the immediate military conflict: that digital infrastructure operated by American corporations is not neutral ground, that no space — physical or digital — is beyond the reach of the conflict, and that the economic architecture underpinning American strategic influence in the region is itself vulnerable.
Taken together, these three motivations suggest that the targeting of data centres was not opportunistic. It was doctrine.
The Structural Vulnerability Nobody Wanted to Acknowledge
The cloud industry has spent two decades building its credibility on a single foundational promise: resilience. Data is replicated. Workloads are distributed. Redundancy is engineered into every layer of the system. If a server fails, another takes over. If a data centre goes offline, traffic reroutes. The architecture is designed to be, in the industry’s favourite phrase, ‘always on.’
That promise was designed for technical failures — hardware faults, software bugs, power outages caused by storms or grid failures. It was not designed for coordinated military strikes targeting multiple facilities in the same geographic region simultaneously.
The structural problem is one of geographic concentration. Cloud providers build regional clusters — groups of data centres within relatively short distances of each other — to reduce latency and serve local customers efficiently. In the Gulf, those clusters are located in a geography that is now an active conflict zone. When multiple facilities within a single region are struck in a coordinated operation, the redundancy architecture that protects against isolated technical failures provides significantly weaker protection.
There is a second, less visible structural vulnerability: the concentration of global cloud workloads among a handful of hyperscale providers. Amazon Web Services, Microsoft Azure, and Google Cloud collectively account for the vast majority of enterprise cloud infrastructure globally. The Gulf facilities that were struck are part of a system on which banks, airlines, hospitals, government agencies, and defence contractors depend. This concentration — which the industry celebrates as efficiency — is, from a security standpoint, a systemic single point of failure at civilisational scale.
Cloud redundancy was engineered for technical failures. It was not engineered for war. The Gulf strikes exposed the gap between those two threat models with brutal clarity.
The incidents have also drawn renewed attention to the physical security assumptions underpinning data centre design. Facilities in the Gulf are heavily fortified against conventional intrusion — biometric access controls, perimeter barriers, private security forces. But they were not designed to withstand drone strikes or precision munitions. The threat model, until now, simply did not include nation-state military action.
The Strategic Geography of Cloud Infrastructure — and Its Discontents
The decision to build major hyperscale cloud regions in the Gulf was driven by compelling commercial logic. The region’s sovereign wealth funds and governments have made artificial intelligence and digital transformation central pillars of their economic diversification strategies. Saudi Arabia’s Vision 2030, the UAE’s AI Strategy 2031, and Qatar’s National Vision 2030 all depend on world-class digital infrastructure. Governments in Riyadh, Abu Dhabi, and Doha have actively courted Amazon, Microsoft, Google, and Oracle — offering regulatory facilitation, land, and in some cases direct investment.
For the technology companies, the Gulf offered access to one of the world’s fastest-growing enterprise markets, sovereign customers with enormous budgets, and a strategic gateway to serve South Asia, East Africa, and the broader Middle East from a single regional hub.
What neither party fully incorporated into its risk calculus was the Gulf’s position at the geographic epicentre of one of the world’s most enduring and volatile fault lines. The region sits adjacent to Iran, shares maritime boundaries with a country that has repeatedly threatened to close the Strait of Hormuz, and hosts the forward military presence of multiple great powers whose interests are not always aligned.
The strikes have now forced a reckoning with that geography. Technology executives who once treated the Gulf’s political risks as manageable background noise — the kind of risk that insurance policies and crisis communications plans could absorb — are now confronting a different category of threat. Military-grade kinetic attacks on data centres do not appear in the standard enterprise risk framework. They do now.
The incident is also generating uncomfortable questions about the concentration of digital infrastructure in other geopolitically sensitive locations. Taiwan — home to TSMC, which manufactures the majority of the world’s most advanced semiconductors — has long been the subject of such concerns. The Gulf strikes add a new dimension: it is not only the manufacturing of digital hardware that is geographically exposed, but the operation of the digital services that run on it.
Infrastructure Warfare: The Emerging Doctrine
Military strategists have long recognised that modern economies are more dependent on interconnected infrastructure networks than at any previous point in history — and that those networks represent high-leverage targets in conflict. The doctrine of ‘effects-based operations,’ developed by US military planners in the 1990s and applied in the Gulf War and Iraq War, identified infrastructure nodes — power grids, communications hubs, transportation networks — as priority targets precisely because their disruption produces cascading effects across an adversary’s entire system.
What is new is the explicit inclusion of commercial digital infrastructure in that targeting calculus.
The Gulf strikes suggest the emergence of what might be termed an ‘infrastructure warfare’ doctrine for the digital age — one that identifies the following as legitimate military targets in a major conflict:
- Hyperscale cloud regions operated by commercial providers
- Submarine internet cables connecting continents and regions
- Satellite internet constellations providing connectivity to contested areas
- AI training clusters and high-performance computing facilities supporting military AI development
- Financial market infrastructure and payment processing networks
- GPS and positioning satellite ground stations
The logic is consistent with established principles of military strategy: degrade the adversary’s ability to coordinate, communicate, process information, and sustain economic activity. In an era where all of those functions depend on digital infrastructure, digital infrastructure becomes the battlefield.
This has profound implications for international humanitarian law and the laws of armed conflict. The legal frameworks governing attacks on civilian infrastructure — the Geneva Conventions, the Hague Regulations, and subsequent protocols — were developed in an era when ‘civilian infrastructure’ meant roads, bridges, hospitals, and power stations. The extent to which those frameworks protect commercial data centres — particularly those that support both civilian and military workloads — is an area of significant legal ambiguity that the international community has not yet seriously addressed.
The laws of armed conflict were written for a world of roads and bridges. The Gulf strikes demand a legal framework for a world of servers and submarine cables.
The Response: Decentralisation, Hardening, and Digital Deterrence
The technology industry’s immediate operational response to the strikes was effective within its existing framework: traffic rerouting, workload migration to unaffected regions, and activation of business continuity protocols. For customers with well-designed multi-region architectures, the disruption was manageable. For those without, it was a costly and clarifying lesson.
But the longer-term strategic response demands more fundamental changes — changes that will be expensive, architecturally complex, and in some cases in direct tension with the efficiency-driven model that has made hyperscale cloud computing commercially dominant.
The first response is geographic decentralisation. If concentrated regional clusters create high-value targets, then spreading infrastructure across a larger number of smaller, more distributed facilities reduces both the impact of any single strike and the attractiveness of the target. This runs counter to the economics of hyperscale computing, which depend on density and concentration to achieve the power and cooling efficiencies that make large data centres cost-effective. The industry will need to absorb higher infrastructure costs if it is serious about resilience in conflict-exposed geographies.
The second response is physical hardening. Data centres in geopolitically sensitive regions will need to be designed to withstand a threat model that now explicitly includes drone strikes, precision munitions, and potentially loitering munitions capable of extended surveillance before attack. This means underground facilities, hardened above-ground structures, sophisticated drone detection and countermeasure systems, and potentially active defence capabilities — raising profound questions about the appropriate relationship between commercial infrastructure and military protection.
The third response is the development of what some analysts are calling ‘digital deterrence’ — the articulation of clear consequences for attacks on digital infrastructure, backed by credible retaliatory capability. NATO has already declared that cyber attacks can constitute an Article 5 collective defence trigger. The Gulf strikes suggest that physical attacks on digital infrastructure operated by alliance members may warrant a similar deterrence framework.
The fourth, and perhaps most consequential, response is a reassessment of where critical digital infrastructure should be built. Governments that have ambitious cloud and AI strategies — and that sit in geopolitically contested regions — must now weigh the economic benefits of hosting hyperscale infrastructure against the strategic risks of becoming a target. That calculus has changed fundamentally since the Gulf strikes.
What This Means for the Global Digital Economy
The Gulf strikes occurred against the backdrop of a global digital economy that has become structurally dependent on uninterrupted cloud services in a way that has no historical precedent. Financial markets execute millions of transactions per second on cloud infrastructure. Supply chain management systems that coordinate the movement of physical goods globally run on cloud platforms. Healthcare records, power grid management, air traffic control, and emergency services increasingly rely on cloud connectivity.
A sustained campaign of infrastructure warfare targeting hyperscale cloud regions — rather than a single incident — would not merely disrupt services. It would fundamentally challenge the operating model of the global economy.
The insurance industry, which has been struggling for years to price ‘cloud outage’ risk, now faces an entirely new underwriting challenge: war risk applied to digital infrastructure. The Lloyd’s of London market, which pioneered war risk insurance for shipping in the 18th century, is already examining whether existing policy language adequately covers kinetic attacks on data infrastructure. The answer, in most cases, is that it does not.
For the technology companies themselves, the strikes raise questions that go beyond engineering and architecture. They raise questions about political risk management, about the obligations of platform companies to the governments of the countries in which they operate, and about the extent to which the infrastructure of the global digital economy can remain in private hands without the explicit protection — and oversight — of sovereign governments.
Some analysts have drawn comparisons to the development of nuclear infrastructure in the Cold War period — civilian technology with dual-use potential, ultimately requiring government involvement in its protection and governance. The comparison is not perfect, but the underlying dynamic it identifies is real: as digital infrastructure becomes critical to national security, the boundary between commercial and strategic infrastructure dissolves.
The Broader Precedent: What Comes After the Gulf
The most significant consequence of the AWS strikes may not be what they destroyed, but the precedent they established.
Before the Gulf strikes, attacking a hyperscale data centre operated by an American technology company was a line that no state actor had crossed in an active conflict. The reputational, diplomatic, and potentially military consequences of such an action were considered prohibitive. That deterrent calculus has now been tested — and the line has been crossed.
If those strikes do not produce consequences that re-establish a credible deterrent against further infrastructure attacks, the precedent is set. Other actors — in other conflicts, in other regions — will draw their own conclusions about whether data centres are legitimate targets. The answer they arrive at will depend heavily on how the international community responds to what happened in the Gulf.
Taiwan is the most frequently cited scenario in private conversations among technology executives and defence analysts. A military crisis in the Taiwan Strait would place at risk not only the semiconductor fabrication facilities that produce the physical hardware underpinning the global technology industry, but also the data centres and connectivity infrastructure of one of the world’s most digitally advanced economies. The Gulf strikes have provided a live case study in what that scenario might look like.
Submarine internet cables — which carry approximately 95 percent of international internet traffic — represent another category of infrastructure whose vulnerability has been dramatically underscored by the Gulf incident. There have already been incidents of suspected sabotage of undersea cables in the Baltic and Red Seas. A coordinated campaign targeting both physical data centres and the cable systems connecting them would represent an entirely new category of infrastructure warfare.
The Gulf strikes answered a question the technology industry hoped would never be asked: yes, data centres are targets. The next question is whether the world will establish rules before the answer becomes routine.
Conclusion: The Cloud Has an Address — and the World Must Respond
The drone strikes on AWS data centres in the Gulf will be remembered as a watershed moment — the day the cloud officially entered the geography of war.
The immediate disruption they caused was significant but manageable. The structural implications are neither. They expose a global digital economy that has been built on assumptions of peacetime resilience, governed by legal frameworks that predate the internet, and protected by deterrence doctrines that did not account for the physical vulnerability of digital infrastructure.
The response demands action across multiple dimensions simultaneously. Technology companies must fundamentally rethink their infrastructure strategies in conflict-exposed regions. Governments must develop legal frameworks that explicitly address the status of commercial digital infrastructure under the laws of armed conflict. International institutions must establish norms — backed by credible enforcement mechanisms — that govern the targeting of civilian digital infrastructure in war. And the insurance, financial, and regulatory systems that underpin the global digital economy must rapidly develop frameworks for a risk category that has moved from theoretical to real.
The Gulf strikes did not change the laws of physics. Servers still need buildings. Buildings still need power and cooling. Power and cooling systems can still be destroyed.
What the strikes changed is the strategic imagination of everyone who builds, operates, regulates, or depends on the global cloud — which is, in the twenty-first century, effectively everyone.
The cloud has an address. It can be found. And as of this conflict, the world knows it can be targeted. The question that now demands an urgent answer is whether the rules, the architecture, and the deterrence frameworks of the digital age are adequate to protect it.
The evidence from the Gulf suggests they are not. The work of making them so has barely begun.
Also Read: Iran War 2026: What Has Happened Since 28 February